
Antonio Russu
Global Head Cyber Security
Securing industrial environments shouldn’t feel like chasing a rare form of magic.
The biggest barrier to robust Operational Technology (OT) security today is not a lack of capability. It’s a trust gap, driven by the belief that OT environments require a completely different type of security professional. This misconception pushes organisations toward ‘OT-only’ specialists and limits access to a wider pool of experienced security practitioners.
The reality is simpler. To secure critical infrastructure, organisations need teams that can bridge IT and OT – applying well-understood security principles through a safety-first methodology that respects the realities of industrial environments.
With NIS2 raising expectations for cyber risk governance across critical services, OT security can’t sit in a specialist silo. Organisations need defensible, safety-first assurance they can explain to leadership and regulators.
The core problem and the real solution
Many organisations are reluctant to engage general penetration testing firms for OT work. The concern is understandable: industrial systems are fragile, outages are expensive, and safety risks are real. But this hesitation is often based on a misunderstanding of the actual security issues.
Most OT vulnerabilities are not exotic or proprietary. They are familiar problems showing up in environments with much higher consequences.
Challenge
- OT pentesting requires ‘special powers’
- Fear of outages or safety incidents
- Gaps between IT and OT teams
Common misconception
- Industrial protocols need unique, proprietary skills
- IT-focused testers will break production systems
- OT security requires control engineers, not security testers
Practical solution
- Apply existing skilled IT pentester skills: adaption of existing TCP/IP tools to OT testing, protocol analysis, attacker mindset
- Use a safety-first, largely passive testing methodology
- Train security professionals on OT priorities and consequences
This is not about inventing a new discipline. It’s about adapting how testing is done.
Why OT security is a CISO priority right now
OT security has moved rapidly up the CISO agenda – not because the technology is new, but because the risk landscape has changed and regulation such as NIS2 is accelerating expectations for governance and resilience.

IT/OT convergence has expanded the attack surface
The idea of an ‘air-gapped’ OT network no longer reflects reality. Remote access, cloud analytics, and predictive maintenance have connected industrial systems to corporate IT networks. When those IT systems are compromised, attackers can move quickly toward operations.
A high-profile example is the Jaguar Land Rover cyber attack, which began as a breach of corporate IT systems and forced the automaker to halt production across multiple factories for weeks in late 2025, costing an estimated £1.9 billion and paralysing the supply chain. This incident shows how IT-side breaches can cascade into OT and operational shutdowns.

The impact of attacks is much higher
An OT incident doesn’t just mean data loss. It can halt production, disrupt supply chains, and create safety risks.
Ransomware and other attacks are surging against critical sectors. Research shows global ransomware attacks against critical industries increased by about 34 % in 2025, with many incidents hitting manufacturing, energy, healthcare and transportation – highlighting that industrial environments are now central targets, not outliers.
These high-impact events underscore why CISOs cannot treat OT security as a niche concern; a single breach can stop production lines, erode revenue and undermine competitiveness.

Regulation is catching up
Across the EU, NIS2 is part of this shift – increasing focus on accountability, risk management and operational resilience for organisations that provide essential services.
Governments and regulators are responding to these high-impact incidents with stronger requirements. In the UK, legislators are advancing the Cyber Security and Resilience Bill, which extends oversight to OT suppliers and managed service providers to raise baseline protections for critical systems.
Similarly, guidance from agencies such as the U.S. Cybersecurity and Infrastructure Security Agency (CISA) now emphasises robust OT asset management and reporting, reflecting a shift from voluntary best practice toward mandated cyber risk governance.
These developments elevate OT security from an engineering concern to a compliance and governance priority at the executive level.
The myth-busting truth: It’s still the same fundamentals
At a technical level, OT security is built on the same foundations as IT security.
It’s basically still TCP/IP
Modern OT infrastructures uses standard Ethernet and the TCP/IP stack at their core. Protocols such as Modbus/TCP, DNP3, Ethernet/IP, and OPC UA sit at the application layer – just like HTTP or SSH. Non-IP based protocols are still used, but often made available to the wider network via gateway devices (e.g. IP to serial, IP to RS485).
If a penetration tester can analyse and manipulate network protocols, they already have the core skill required for OT. The questions don’t change:
- What is this protocol designed to do?
- How could it be misused?
Familiar vulnerabilities, bigger consequences
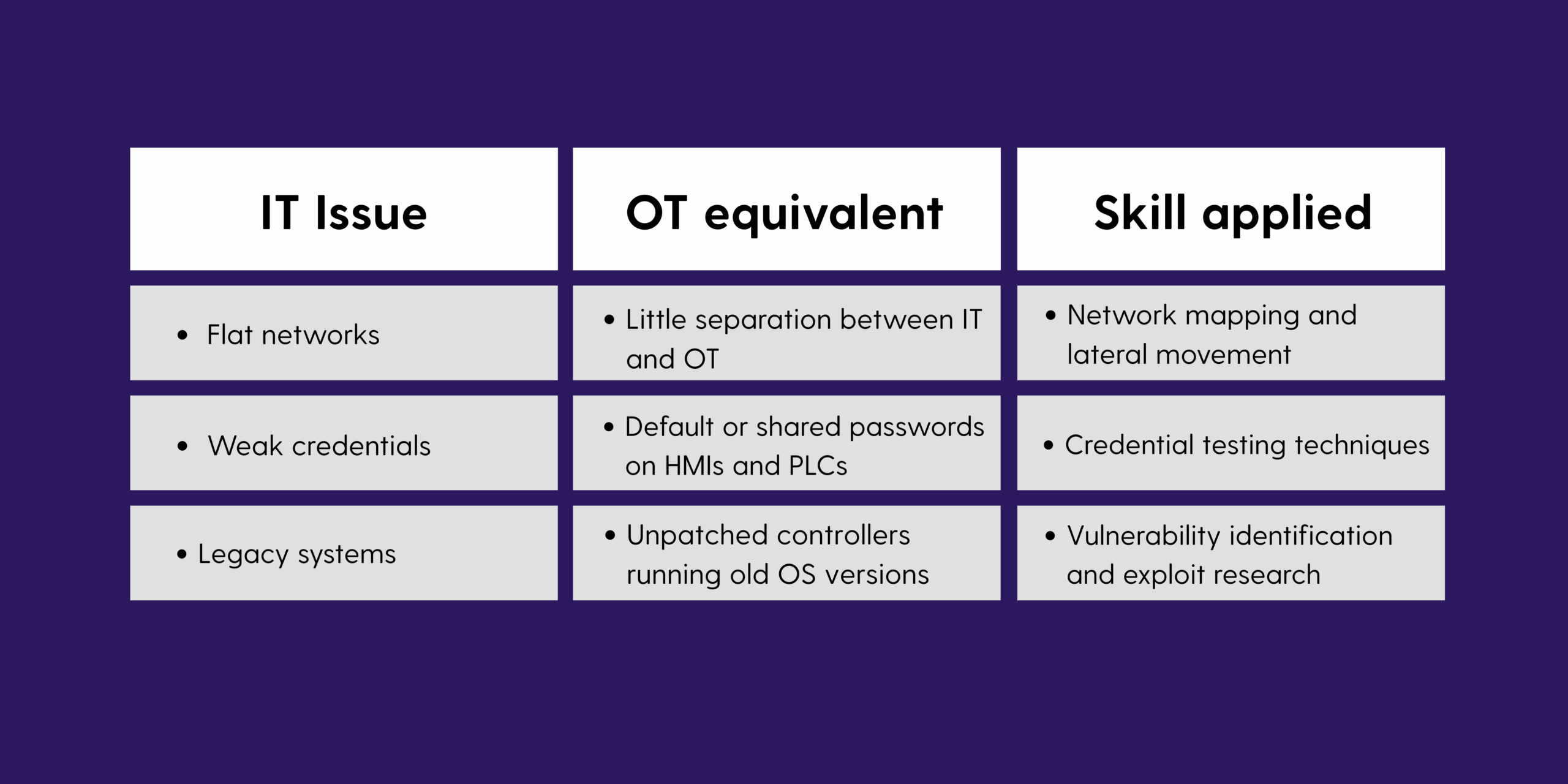
The difference is not complexity – it’s impact.
The essential shift: Safety and methodology
Where OT security truly differs is in how testing is performed.
Done well, a safety-first methodology also creates repeatable, auditable assurance: clear scope, agreed risk boundaries, and documented decisions about what was tested (and what was deliberately not).
A different priority order
- IT: Confidentiality → Integrity → Availability
- OT: Safety → Availability → Integrity
In OT, safety always comes first.
The golden rule of OT penetration testing
Replace aggressive exploitation with careful, controlled analysis.
Passive testing first
Asset discovery and network mapping should be based on passive monitoring via SPAN/TAP ports and OT-aware tools. Aggressive scanning can destabilise or crash legacy equipment.

Understand command impact
Testers must understand which protocol actions can stop processes or create safety risks. High-risk actions should only be performed in controlled lab environments and with explicit operational approval.

This isn’t about avoiding testing – it’s about doing it responsibly.
Bridging the IT/OT divide
The belief that only ‘OT-exclusive’ firms can safely work in industrial environments limits an organisation’s defensive depth.
Resillion bridges the IT/OT divide by combining deep offensive security expertise with a safety-centric operational framework designed for OT. Our approach applies proven penetration testing skills through controlled, risk-aware methodologies that respect the fragility and importance of the plant floor.
OT security doesn’t require special powers. It requires the right mindset, the right process, and an uncompromising focus on safety.
As NIS2 pushes cyber risk into the leadership spotlight, that mindset and process matter as much as tooling – because you need assurance you can evidence, not just intentions you can describe.
For more information visit our penetration testing services web pages.


