
Antonio Russu
Global Head Cyber Security
In many boardrooms, cyber security conversations still revolve around ransomware, phishing and data breaches. But the potentially more damaging risk of remote kill switches is emerging.
Embedded in connected devices, from fleets to sensors, cameras, controllers and smart-city assets, kill switches aren’t vulnerabilities or configuration issues – they’re deliberate features built deep into firmware or hardware. And they’re designed to change how a device behaves, sometimes without the owner’s knowledge or control.
Because connected devices sit at the centre of expanding modern infrastructure, they mean that many organisations don’t fully control the technology they depend on.
A wake-up calls for senior leaders
In a worrying trend, kill-switch concerns are now emerging in systems that once seemed routine and dependable. It’s becoming clear that many connected devices contain undocumented or poorly understood remote-access pathways controlled by the manufacturer.
In the UK, for example, the Department for Transport and the National Cyber Security Centre are investigating whether hundreds of Yutong electric buses could be remotely disabled by their manufacturer, raising questions about operational control in public transport. Similar concerns have surfaced in mainland Europe, where unexplained behaviour in city camera networks has prompted deeper analysis of the underlying technology.
For senior leaders, the message is clear: If a device you depend on can be switched off remotely, it becomes a business-critical risk.
How kill switches impact your organisation
For senior decision-makers, the implications go beyond technical failure. Kill-switches have practical, business-level consequences that affect core parts of your business, including:
Understand your risk
Effectively addressing the risk of kill switches means assessing your organisation against all levels of risk, including accidental exposure, malicious software kill switches and malicious physical kill switches.
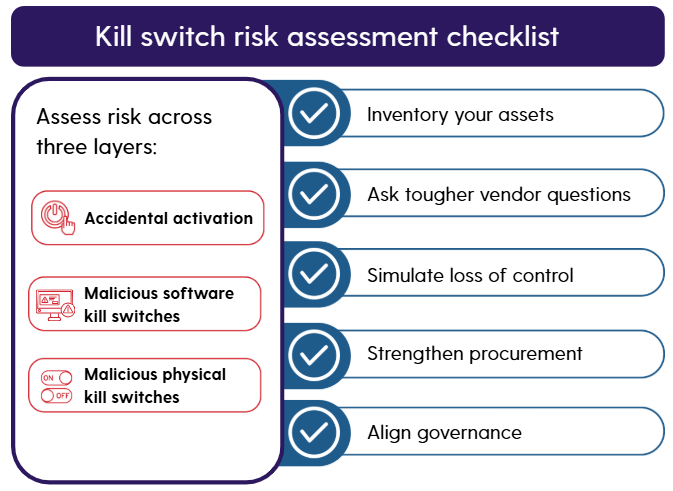
To assess your exposure across all three levels, follow a comprehensive kill-switch checklist, including:
Map connected devices across fleets, facilities and networks. Identify which have remote-management or OTA update capabilities.
Determine who holds credentials, how access is logged and whether remote commands can be isolated or disabled.
Run “kill-switch simulations” with engineering and risk teams to understand how systems behave when connectivity fails, remote commands stop responding or unknown device functions activate.
Build transparency requirements into contracts, with the ability to audit or lock down critical pathways and mandate disclosure of remote-access mechanisms and firmware behaviour, including fallback modes that maintain core operations.
Ensure cyber, operations and procurement teams understand the risk and address it collectively. Kill-switch exposure should feature at board or C-suite level, tied into operational-resilience and continuity plans.
Go beyond conspiracy to effectively mitigate risk
There are several misconceptions about kill switches, including the idea that entire fleets could be shut down at once, that all kill switches are malicious or that the issue relates to one country. Remote-access paths may exist, but wide-scale shutdowns require specific conditions. Many channels support diagnostics or updates, and the real risk comes from misuse or exploitation. Scrutiny now extends across multiple regions.
Managing the risk means moving beyond these myths. It demands senior-level engagement and awareness that kill switches post a structural risk that can undermine operational continuity, regulatory compliance and public trust.
Kill switches in modern connected systems aren’t science fiction. Recent cases show how quickly a maintenance feature can become an existential point of failure. And by the time a kill switch activates, it may be too late to mitigate the harm this can cause.
Securing your organisation means treating kill-switch risk as an operational priority, not an afterthought.
How Resillion can help
At Resillion, we help organisations identify and address hidden kill-switch risks. Our work combines device-level assessment, firmware analysis and operational resilience planning. Drawing on practical experience, including investigations into anomalous behaviour in city camera networks, we help organisations:
- clarify whether kill-switch logic exists
- identify who controls it
- simulate activation scenarios
- design fallback modes that keep services running
- strengthen procurement and supply-chain governance
Visit our cyber services web pages to find out how Resillion can help you to gain the clarity and assurance needed to protect essential operations and strengthen long-term resilience.


